The Signet Team brings together engineers, consultants, and technical staff from Signet CS — a company that has been helping businesses across Serbia design, build, maintain, and protect their IT infrastructure since 2005. Our articles draw on day-to-day work with business systems, Microsoft environments, networks, hosting, and cybersecurity.
Signet Team
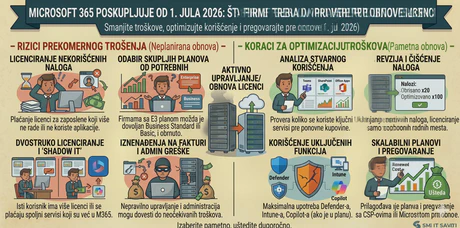
Microsoft 365 Price Increase from July 1, 2026: What Companies Should Check Before Renewing Licenses
Microsoft 365 has become a core tool for daily work in many companies: business e-mail, Office applications, Teams meetings, OneDrive, SharePoint, account security, and document access. Because of this, a change in Microsoft 365 license pricing is not just an administrative detail. It directly affects the IT budget and the way a company uses its digital tools.
Read More
How to Know Your IT Infrastructure Has Outgrown Its Current Setup
IT infrastructure rarely becomes outdated overnight. It gradually becomes slower, harder to maintain, and less aligned with the way a company actually works. Computers still turn on, servers still run, and the network “mostly works” — but problems start appearing more often: users wait longer, applications slow down, backups take too much time, and every new change becomes a risk.
Read More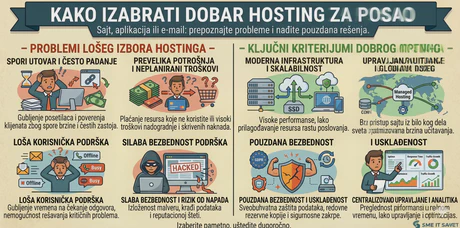
How to Choose Good Hosting for a Business Website, Application, or E-Mail Service
Hosting is often chosen only when a website needs to be published quickly or when the existing provider starts causing problems. In those situations, companies usually compare price, disk space, and number of e-mail accounts. However, for a business website, application, or e-mail service, hosting is not just a technical service. It directly affects availability, speed, security, and user trust.
Read More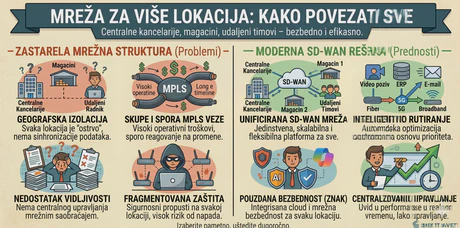
Network for Multiple Locations: How to Connect Offices, Warehouses, and Remote Teams
When a company operates from a single location, the network is relatively simple: internet connection, local network, Wi-Fi, servers, printers, computers, and users. However, as soon as additional offices, warehouses, retail locations, remote workers, or field teams appear, the network becomes a much more important part of the business.
Read More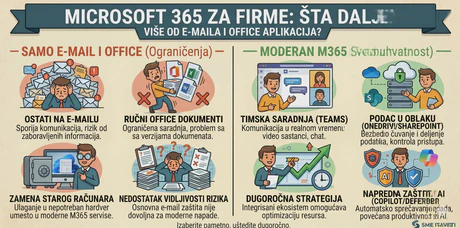
Microsoft 365 for Business: More Than E-Mail and Office Applications
For many companies, Microsoft 365 is still synonymous with Outlook, Word, Excel, and business e-mail. And these are important parts of the platform. But today, Microsoft 365 is much more than a set of office applications. When implemented properly, it can become the central place for communication, collaboration, security, document management, and protection of business data.
Read More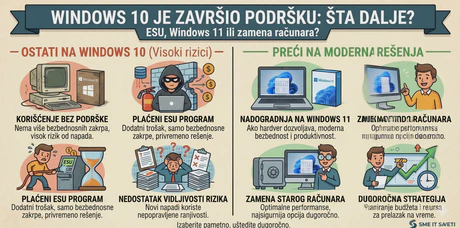
Windows 10 Support Has Ended: ESU, Windows 11, or Replacing Computers?
Windows 10 was the standard in business environments for many years. Many companies still use it because it is stable, familiar to users, and compatible with existing applications. However, Microsoft officially ended support for Windows 10 on October 14, 2025. After that date, Microsoft no longer provides standard technical support, feature updates, or security updates for Windows 10 computers.
Read More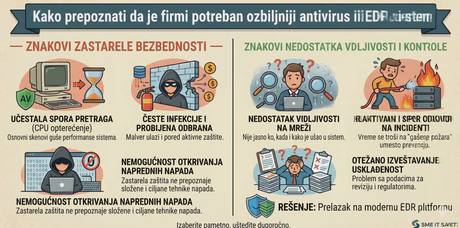
How to Know Your Company Needs a More Serious Antivirus or EDR System
Many companies still believe that traditional antivirus protection is enough to protect their computers. That may have been closer to the truth in the past, but today’s threats are much more complex. Attacks no longer come only through infected files. They come through phishing e-mails, compromised accounts, malicious links, remote access tools, macros, fake invoices, vulnerable applications, and legitimate system processes that are abused.
Read More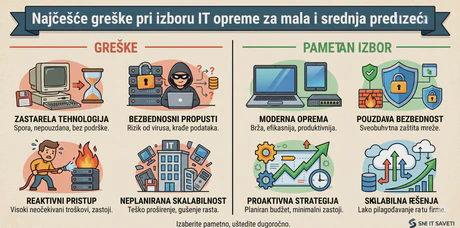
The Most Common Mistakes When Choosing IT Equipment for Small and Medium-Sized Businesses
Buying IT equipment often looks simple: you need a new laptop, server, network device, printer, or storage system, so you compare prices and choose what seems affordable. However, for small and medium-sized businesses, the wrong equipment choice can later create much higher costs than the initial savings.
Read More